In April 2026, the cybersecurity landscape quietly crossed a threshold.
With the introduction of Claude Mythos Preview, a model capable of identifying thousands of vulnerabilities across major operating systems, we are no longer dealing with incremental improvements in security tooling we are witnessing a fundamental shift in how vulnerabilities are discovered, weaponized, and defended against.
This shift demands a rethink of how organizations approach Security Posture Management (SPM). Static audits and periodic scans are no longer sufficient. In the era of Mythos, continuous, real-time security validation, patching, and remediation is the only viable strategy.
The Mythos Moment: When Attack Speed Outpaces Defense
Historically, security teams operated on a lag:
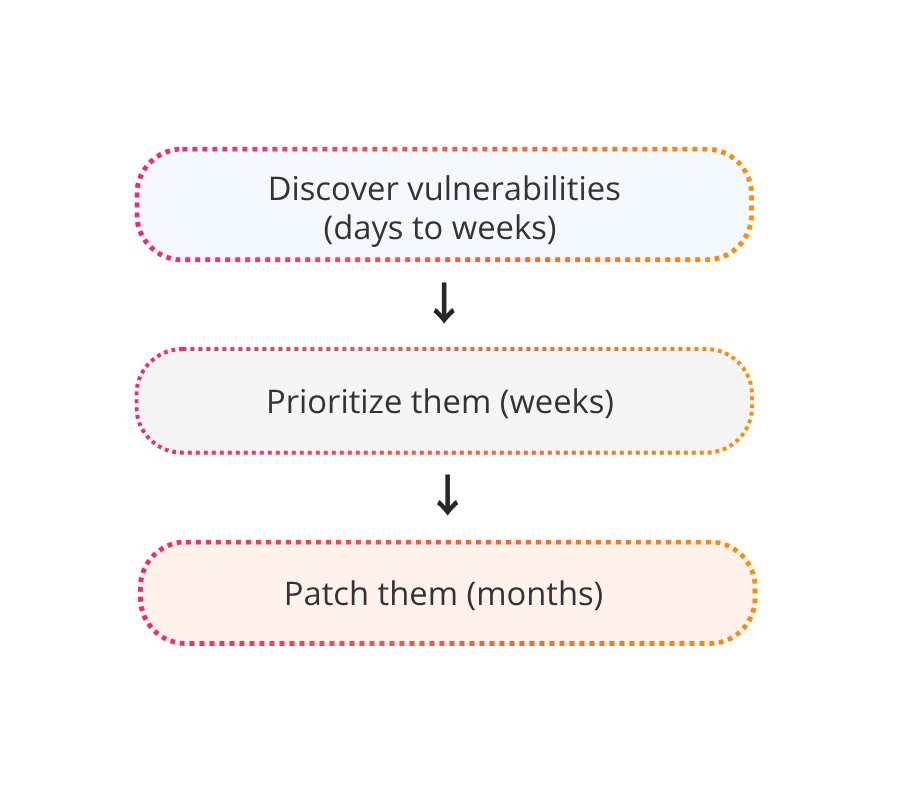
That model is now obsolete.
AI systems like Mythos can:
- Scan vast codebases and infrastructure configurations in minutes
- Identify deep, non-obvious vulnerabilities
- Simulate attack paths across complex environments
This means attackers can:
- Discover zero-days faster
- Chain vulnerabilities more effectively
- Launch exploits at unprecedented speed
The asymmetry has flipped.
Security Posture Management: From Snapshot to Streaming
Traditional security posture management was built around snapshots:
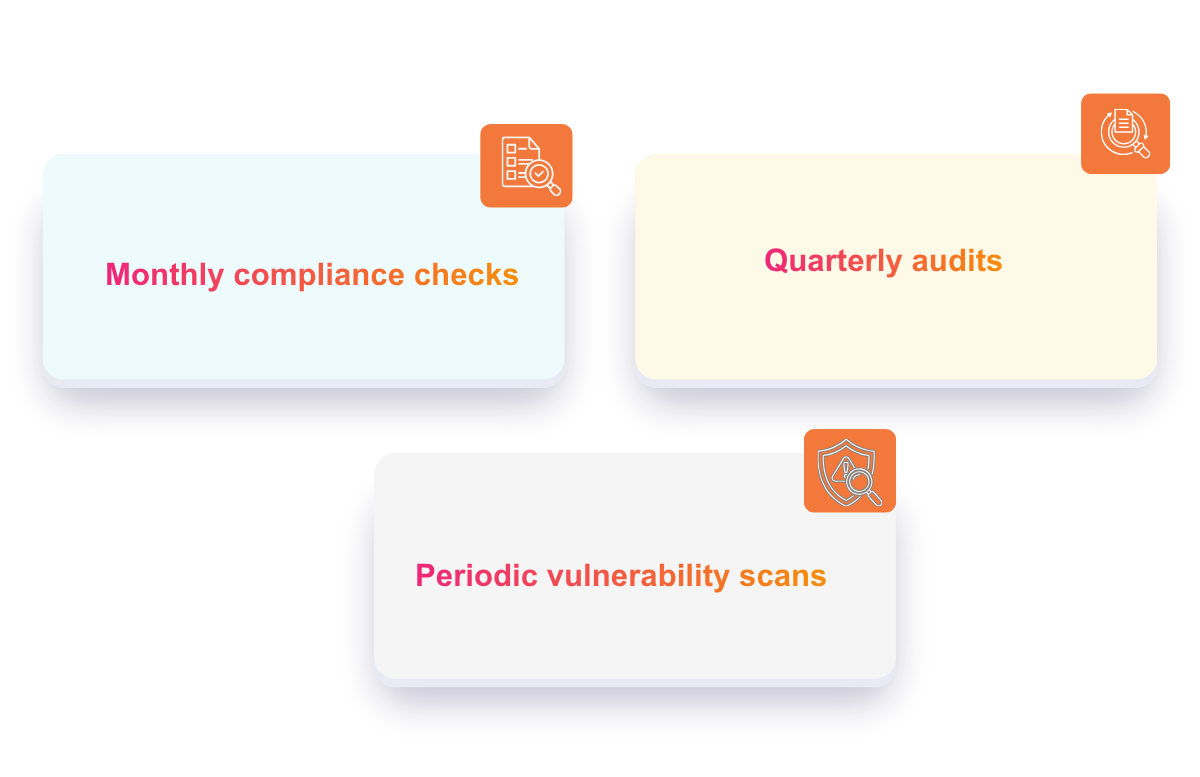
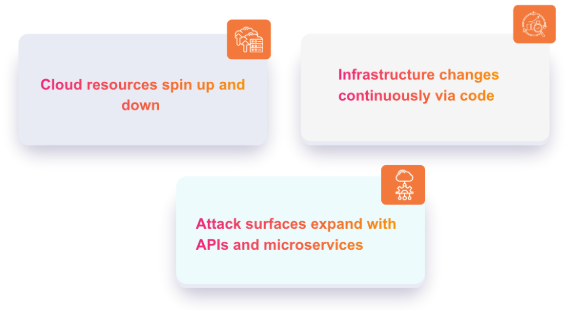
But modern environments are dynamic:
In this context, posture is not a state—it’s a continuous stream.
What Modern SPM Must Become
To survive in the Mythos era, SPM must evolve into:
- Continuous Visibility
Every asset, misconfiguration, identity risk, and exposure must be tracked in real time. - Context-Aware Risk Prioritization
AI-driven systems must determine:- What is exploitable
- What can be chained
- What truly impacts the business
- Continuous Patching & Automated Remediation
This is where most organizations still fall short.
- Continuous and risk-driven
- Integrated into runtime and pipelines
- Automated wherever possible
Because unpatched vulnerabilities are no longer "eventual risks" they are immediate entry points.
Real-Time Checks: The New Security Baseline
If Mythos represents real-time offense, defense must match it.
Continuous Checks Enable:
- Immediate detection of misconfigurations
- Drift detection from secure baselines
- Live compliance enforcement
- Real-time attack surface monitoring
But detection alone is not enough.
Real-Time Fixes and Continuous Patching: Closing the Window of Exploitation
Detection without action is noise. And patching without speed is ineffective.
In the Mythos era, the goal is clear:
Shrink the window between discovery and fix to near zero.
What This Looks Like in Practice:
- Vulnerability discovered → Patch applied automatically or queued instantly
- Misconfigured resource → Auto-corrected in real time
- Vulnerable container → Rebuilt with patched base image and redeployed
- Outdated dependency → Updated directly in CI/CD pipeline
This approach combines:
- Runtime fixes
- Pipeline-integrated patching
- Policy-driven remediation
The result?
- MTTR drops from days to seconds
- Exposure windows nearly disappear
- Security becomes proactive instead of reactive
Why Continuous Checks + Patching + Fixes Are Non-Negotiable
In a Mythos-driven world:
- Attackers don’t wait for patch cycles
- Exploits can be generated instantly
- Compliance audits don’t reflect real-time risk
Only continuous enforcement ensures:
- Always-updated systems
- Minimal exposure to known vulnerabilities
- Consistent security across dynamic environments
The New Ethos of Security
The emergence of Mythos signals a broader shift:
Security is no longer about finding vulnerabilities.
It’s about fixing and patching them before they can be exploited.
This requires a move toward:
Final Thoughts: From Reactive to Autonomous Security
The era of Mythos forces a hard truth:
You cannot secure modern systems with delayed patching and periodic checks.
Security posture management must evolve into:
And critically:
Deeply integrated with continuous patching and instant remediation workflows
Organizations that embrace this shift will operate with resilience by design.
Those that don’t will be trying to patch vulnerabilities
after they’ve already been exploited.
The Missing Layer: Execution
Most teams already have visibility.
What they lack is real-time execution.
Security today demands a unified approach that connects posture insights directly
to automated fixes and continuous patching across the entire cloud stack.
Platforms like Banyan Cloud are helping close that gap—turning security from observation into immediate action.