We use cookies to improve your browsing experience on our website, to show you personalized content and targeted ads, to analyze our website traffic, and to understand where our visitors are coming from Learn more.
A Cloud Workload Protection Platform (CWPP) is critical for organizations operating in cloud environments. It delivers tailored security for virtual machines, containers, and serverless workloads protecting against evolving threats in dynamic, distributed infrastructures. As cloud adoption accelerates, CWPP ensures consistent visibility, compliance, and threat mitigation across your cloud-native applications.
Auto discovery of all workloads across multi clouds and on-premises and integration with DevOps pipelines
Offers real time risk assessment and prioritizes remediation based on exploitability and impact
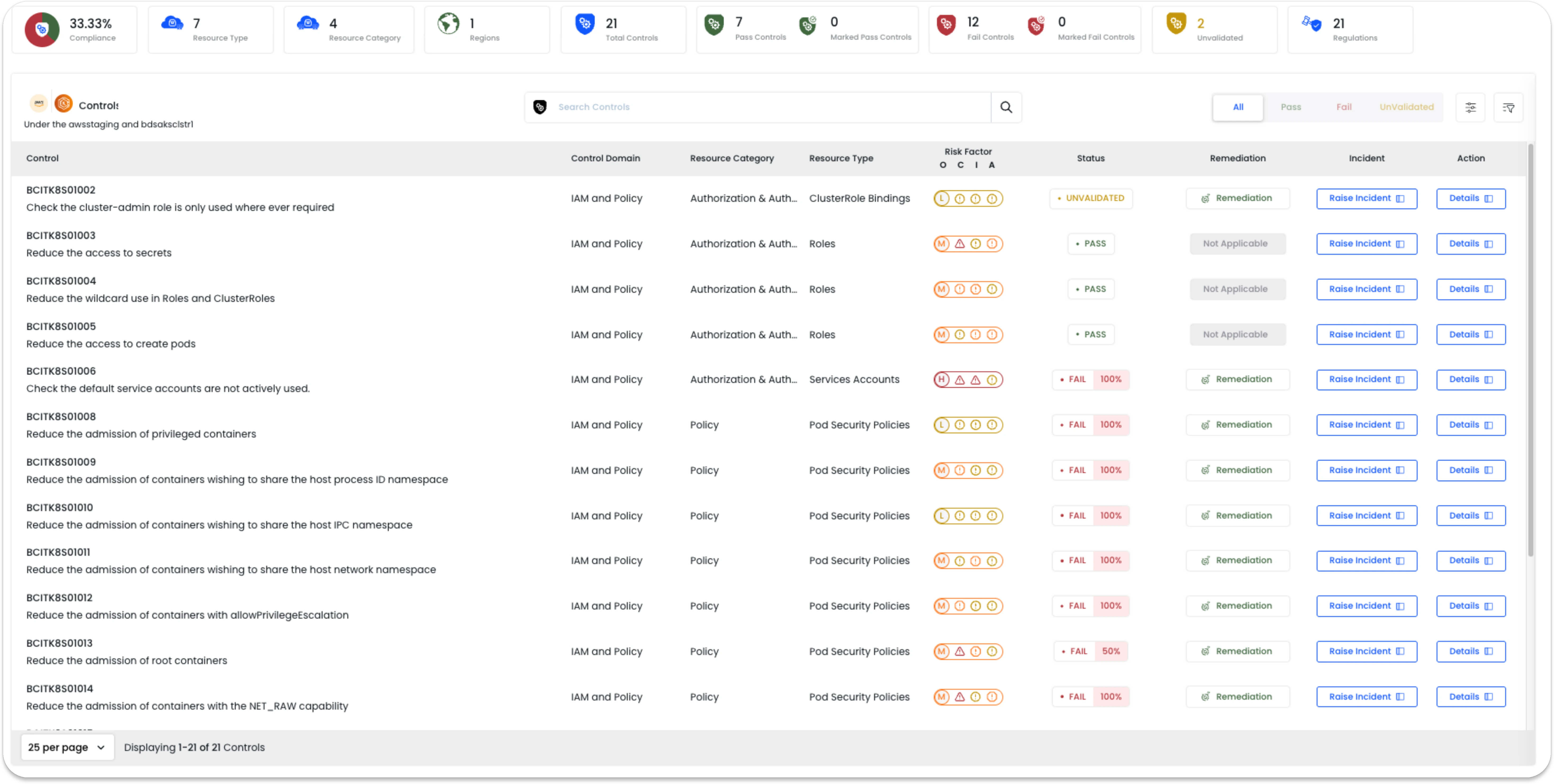
Continuous configuration assessment of misconfiguration against the Regulatory standards with auto remediation capabilities.
Modern workloads are highly distributed across public cloud, private cloud, hybrid, and on-premises environments. Legacy security tools can’t scale with the speed and complexity of today’s application delivery.
Our solution provides a posture aware, agentless security layer that protects your workloads without operational friction while addressing both infrastructure and data layer risks.

Instant visibility and protection—no agents, no downtime. Our platform scans cloud and on-prem environments seamlessly, simplifying deployment and minimizing management overhead.
Protect workloads across AWS, Azure, GCP, OCI, Kubernetes, containers, virtual machines, and on-premises infrastructure all from a single control plane.
Correlate misconfigurations, excessive permissions, and risky services at the cloud configuration level with actual workload behavior for prioritized risk remediation.
Go beyond infrastructure scanning. Understand what your workloads are running, and protect applications and services from misuse, drift, or exploitation.
Identify security gaps, misconfigurations, and access risks in cloud and on-prem databases. Automatically audit critical database actions and monitor real-time access patterns.
Continuously identify known vulnerabilities, zero-days, and suspicious activity backed by threat intelligence and behavior based alerts.
Ensure least privilege enforcement across human and machine identities with granular policy controls and integration with cloud-native IAM.
Advance Governance capabilities
Multi Cloud Security Posture
Cloud Entitlement for Zero trust (Enforcement)
Global and Regional Regulations support
Advanced Customizations
Point in time security posture in past
Auto remediation options
Built in Service management
Export Audit Reports
Geo based RBAC for Security posture
Agentless monitoring
Banyan Cloud is a Cloud Security SaaS by extending CNAPP solution to hybrid environments, ensuring comprehensive security posture management for public clouds, private clouds and data workloads across on-premises infrastructure
Security Controls
Cloud Platforms
Regulations supported
Database Technologies